Detection System of Record
A Detection System of Record introduces a new architectural layer in modern security operations.
It governs detection effectiveness across the continuous threat-to-detection operating loop — from initial threat identification through validation, live operation, and structured improvement.
Operating above SIEM, EDR, BAS, and CTI systems, it does not execute detections. It defines how detection effectiveness is measured, validated, and improved across them.
Security tools execute. A Detection System of Record governs detection health.
Security Has Tools. It Lacks a Detection System.
Modern security operations rely on specialised systems: SIEM stores and searches logs. EDR produces alerts. BAS validates controls. CTI provides intelligence. Detection engineering builds rules.
What does not exist in most environments is a persistent governance layer that connects these systems into a single operational model — one that unifies threat intelligence, detection logic, incident outcomes, and validation results.
Without that layer, detection effectiveness is inferred from individual tools rather than governed as a system.
The Full Threat-to-Detection Operating Loop
A Detection System of Record governs detection effectiveness across a continuous operating loop — not a linear workflow.
- Threat — A threat is identified through intelligence, adversary behaviour, or emerging risk.
- Validation — The organisation validates its current posture using BAS or simulation to determine whether detection or prevention capability already exists.
- Detection — Where gaps are confirmed, detection logic is engineered and implemented across relevant tools.
- Live Signals — Detection moves into live operation. Real telemetry, alerts, and operational outcomes provide measurable signal.
- Improvement — Detection logic is refined, tuned, matured — or decommissioned — based on validation results and operational evidence.
Improvement feeds back into threat understanding, restarting the loop.
The Detection System of Record governs this entire cycle — providing persistent, system-level visibility across decision, implementation, live operation, and refinement.
The loop below illustrates how detection effectiveness is governed — from initial threat identification through validation, live operation, and continuous improvement.
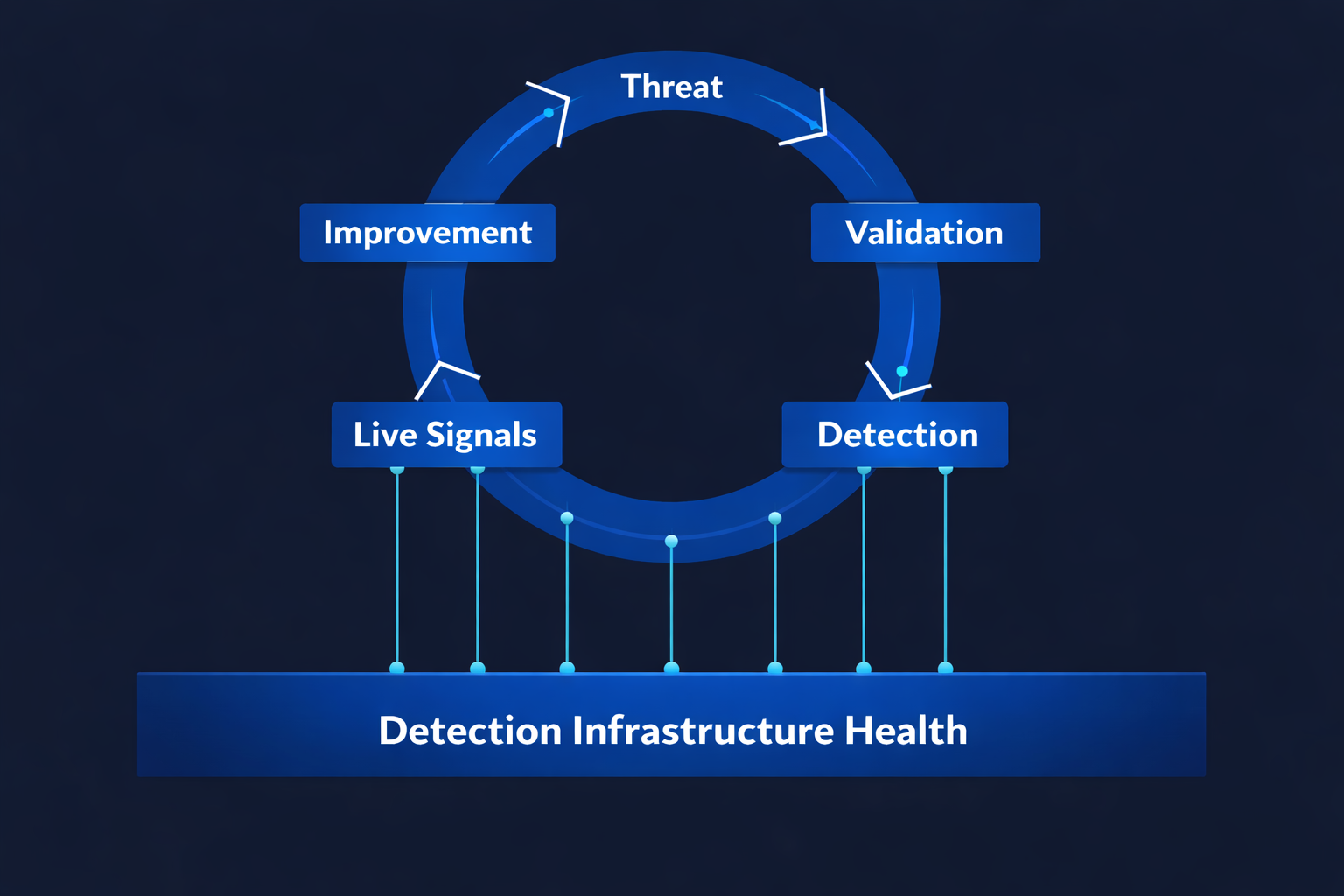
The Foundational Layer: Detection Infrastructure Health
Detection effectiveness is not determined solely by detection logic. It is dependent on the operational health of the underlying security and telemetry infrastructure.
SIEM pipelines, endpoint agents, log ingestion flows, data normalisation, rule execution engines, and validation tooling are typically monitored in isolation — by different teams, using different metrics.
Yet detection performance depends directly on their stability, integrity, and reliability.
If telemetry is incomplete, if agents are degraded, if ingestion pipelines drop events, or if rule execution is impaired, detection effectiveness deteriorates — even when detection logic appears correct on paper.
This foundational dependency is rarely governed as part of the detection operating model.
A Detection System of Record extends governance beneath the operating loop to incorporate infrastructure health as a first-class input into detection effectiveness.
Infrastructure reliability, telemetry integrity, and platform drift are continuously assessed in context of detection performance — not as separate operational metrics, but as determinants of detection health.
Detection logic cannot be healthy if the infrastructure that executes it is not.
In this model, detection health cannot be considered in isolation from the systems that enable it.
A Governance Layer — Not Another Execution Tool
A Detection System of Record operates at the architectural layer above security tools. It does not execute detections. It governs how detection effectiveness is measured, validated, and improved across them.
Modern security operations are composed of specialised systems, each optimised for a specific domain:
SIEM platforms aggregate telemetry and execute detection logic
to generate alerts.
EDR platforms monitor endpoint behaviour and enforce detection
or prevention controls.
BAS platforms simulate adversary techniques to validate control performance.
CTI platforms provide adversary intelligence and contextual threat insight.
Detection engineering tooling supports authoring and deploying detection logic.
Each of these systems executes within its own domain. None provides persistent, system-level governance across them.
A Detection System of Record introduces that missing layer. It unifies threat intelligence, detection logic, validation outcomes, live operational signals, and improvement cycles within a single operational model — governing detection effectiveness across tools rather than within a single tool.
Execution remains in SIEM, EDR, and enforcement platforms. Validation remains in BAS. Intelligence remains in CTI. The Detection System of Record governs how these domains align, measure performance, and improve over time.
Category Boundaries
A Detection System of Record is distinct from adjacent security domains. It does not compete with them; it governs detection effectiveness across them.
It is not a SIEM, which focuses on telemetry ingestion and alert generation.
It is not an EDR, which enforces behavioural detection and prevention at the endpoint.
It is not a BAS platform, which validates control performance through simulation.
It is not a CTI system, which provides adversary intelligence.
It is not a detection engineering IDE, which supports rule authoring and deployment.
It is not an exposure management or CTEM framework, which prioritises exploitable risk.
Those systems execute, simulate, prioritise, or respond. A Detection System of Record governs how detection effectiveness is persistently measured, linked across the operating loop, and continuously improved.
The Operating Model for Detection as a Managed Capability
A Detection System of Record does more than connect tools. It defines the operating model by which detection is treated as a governed, measurable capability within security operations.
In many organisations, detection exists as distributed logic embedded in SIEM rules, endpoint controls, and monitoring playbooks. Ownership is fragmented. Validation is periodic. Performance is inferred from incident response rather than measured as a capability with defined health.
The DSoR introduces structural accountability. Detection capability is baselined. Validation results are linked to specific detection logic. Infrastructure health is incorporated into performance measurement. Live signal quality becomes observable. Maturity progression and drift are tracked over time.
Detection effectiveness becomes a governed system capability — not a by-product of tooling.
In this model, security operations move from reactive monitoring to managed detection health across the continuous operating loop.
Why It Matters
Modern security architectures have execution systems, validation systems, and exposure prioritisation frameworks. The Detection System of Record introduces a governance layer that connects them into a coherent operating model.
Without a Detection System of Record, coverage is assumed, validation is episodic, and detection effectiveness cannot be persistently governed.
With a DSoR, detection effectiveness becomes a governed system capability — persistently measured, traceable across the operating loop, and continuously improved.