Detection Coverage: Why Rule Counts Mislead Security Leaders
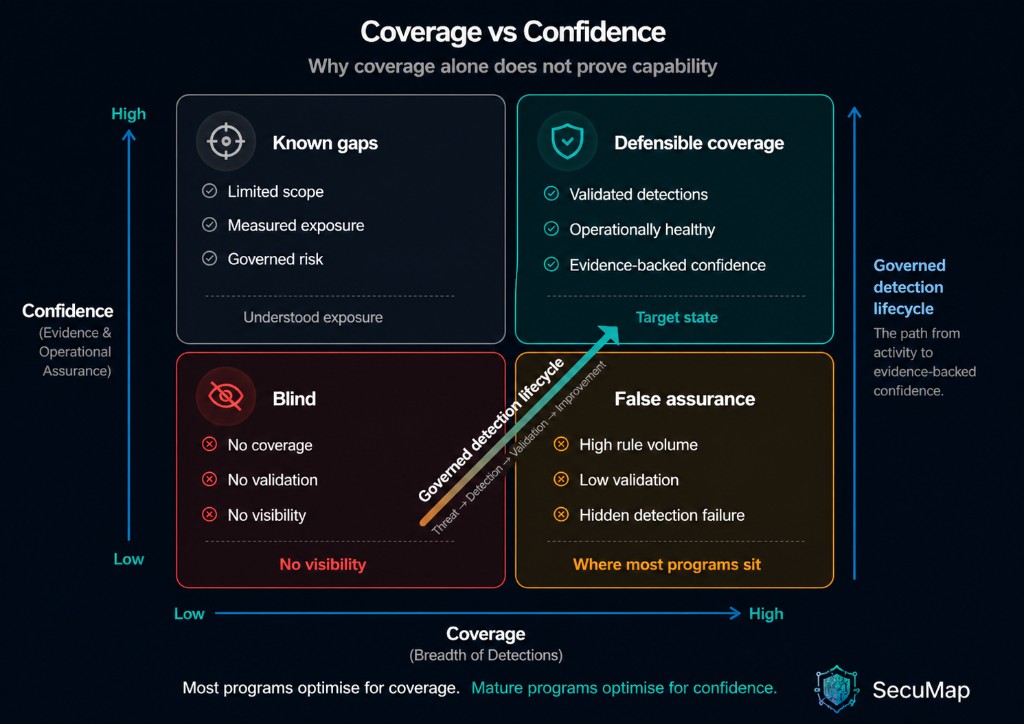
Most security programs cannot prove they are protected against the threats that matter. Instead, leadership is offered coverage built from rules shipped, techniques mapped, and controls deployed. These are signals of activity, not proof of capability. They can read as “we are in good shape” while capability is eroding in production. That is not a spreadsheet error; it is a confidence problem in the reporting model. When those signals are taken as proof, investment and attention follow the map, not the real risk—and weakness often stays hidden until an incident makes it obvious.
Coverage without governance does not just mislead—it can hide failure. Strong-looking coverage can sit alongside undetected loss of health: telemetry drops, scope narrows, validation stales, and the control environment drifts—while the headline metric barely moves. False assurance is the predictable outcome, and with it, misdirected spend and a delayed understanding that detection is no longer doing what the board deck implies.
The heart of the issue is simple to state and hard to manage: volume is not the same as quality, and a large rule base does not prove healthy, validated, useful detections in real incidents. Mature teams separate declared (logic exists and is mapped), validated (tested against representative behavior), and operational (proven healthy in production and producing reliable outcomes). Blurring those states lets organizations report comfort while the ground shifts.
A technique can remain “covered” on paper when the underlying detection has already failed in practice—for example, a parser that stopped parsing correctly two weeks ago. The rule still exists, the report still counts it, but the path from evidence to reliable alert is broken. Until something forces that truth into the open, coverage stays green; confidence does not.
From coverage metrics to a governed capability
The fix is not a better chart. Coverage has to be governed as a system, not as a set of one-off metrics. That means a closed loop: threat and priority context, the detection logic in scope, validation evidence, operational health, and learnings that drive the next change—all tied so the organization can see whether claims are still true this week.
A Detection System of Record (DSoR) — the model that governs coverage, validation, and production proof in one auditable lifecycle — is what makes that work: a single, auditable thread linking threat intelligence, detection logic, validation, and real outcomes. It makes visible where confidence is proven, where it is only assumed, and what to fix first. That requires treating detections not as static text in a library, but as governed assets—with ownership, performance and validation history, dependencies, and operational context that survives handoffs. Without that, detections behave like unmanaged code—deployed once, rarely revalidated, and assumed to work indefinitely.
SecuMap is a Detection System of Record (DSoR) — a vendor-neutral governance layer that continuously maps threat intelligence to detection coverage, measures detection effectiveness, and governs detection health across the full threat-to-detection operating loop. In other words, SecuMap is where that system lives: evidence, health, and accountability for detection—above your SIEM, EDR, BAS, and CTI, not in place of them.
When coverage is run this way, reporting stops being a vanity metric and starts steering work: which assumptions are current, which controls are drifting, and which investments change measurable risk—with traceability, not hope.
Where programs break—and the consequence
Ownership fragmentation. Intelligence maps threats, engineering writes rules, SOC triages—but if nothing governs the thread from priority to production behavior, you lose the traceability between threat, detection, and outcome. Coverage becomes unauditable, and decisions are made on assumptions that cannot be verified. The story you tell in review does not have to be the one that is true in the environment.
Validation isolation. When BAS, purple team, and lab results live outside the lifecycle, known gaps can stay open while the dashboard still shows “breadth.” The business risk is a growing portfolio of known blind spots you already paid to find—with no enforced path to closure.
Infrastructure blindness. If coverage ignores data quality, parser integrity, and sensor health, you are measuring content while the substrate rots. A control can be logically right and operationally null when the pipeline is sick—and the failure mode is often silent until something breaks hard enough to notice.

How to improve without adding noise
If your coverage signal does not move when validation fails, telemetry rots, or a parser silently breaks, the model is not measuring reality—it is narrating comfort. Work from risk-prioritized scope, not a race to “fill” a framework. Define per-behavior confidence criteria—including validation and operational quality—and govern lifecycle state: ownership, change history, dependencies, and when drift must force work, not a footnote in a report. Tie backlog and leadership reporting to confidence impact, not only how much content you ship. If a monthly number does not change what engineering or the SOC does next, it is decoration, not control.
What to take back
Coverage is not a percentage to report—it is a capability to govern. Until it is bound to validation, health, and operational outcomes, the organization will keep producing confidence without assurance. The shift is not “more detections.” It is treating detection as a system—with evidence, measurability, and ownership from threat focus through to what actually fired in your environment. When you want to move from reported coverage to provable capability, see the SecuMap workflow in action or request an executive briefing for a leadership walkthrough.