SecuMap — Detection System of Record (DSoR)
SecuMap is a Detection System of Record (DSoR) — a vendor-neutral governance layer that continuously maps threat intelligence to detection coverage, measures detection effectiveness, and governs detection health across the full threat-to-detection operating loop. For the category story before platform detail, read what is a Detection System of Record?
The platform implements the governance mechanisms required to persistently measure, monitor, and improve detection health across the continuous threat-to-detection operating loop.
Operating at the architectural layer above security tooling, the platform governs detection health across execution systems, validation platforms, and underlying infrastructure — instrumenting performance without executing detections itself.
How Detection Health Is Governed
A Detection System of Record requires structured governance across decision, execution, validation, live operation, and improvement. The SecuMap platform implements these governance controls through measurable health indicators, cross-domain traceability, and continuous feedback loops.
Detection health is not inferred — it is instrumented, measured, and governed.
See SecuMap in action
Explore a hosted demo environment with sample data — MITRE views, use-case lifecycle, and governance patterns — before you deploy SecuMap yourself.
Platform views
Tactical and strategic visibility in one product
MITRE ATT&CK effectiveness
Live visibility into adversary technique coverage and efficacy — aligned to deployed rules, not vendor marketing maps.

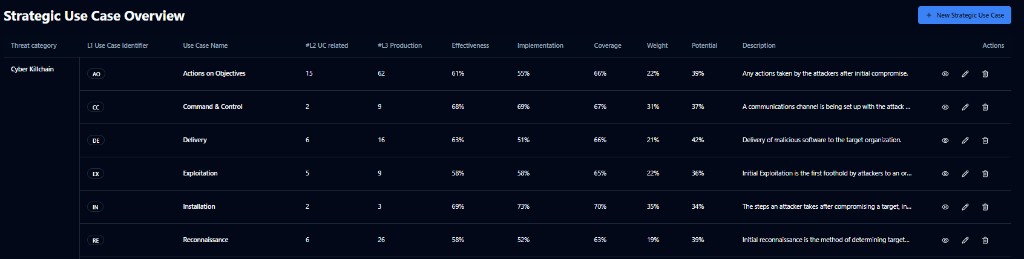
Lifecycle governance from threat intelligence through logic authoring and control validation — use-case maturity in one place.
MaGMa-aligned use-case maturity
Operationalise Management, Growth, and Metrics & Assessment so priorities are defensible and traceable across teams.
How the platform delivers governance
Lifecycle Traceability
SecuMap unifies threat intelligence, detection logic, validation outcomes, live operational signals, and infrastructure health within a single operational model.
Persistent Measurement
Detection health is measured continuously rather than inferred periodically — with visibility into coverage, validation state, execution stability, and infrastructure reliability.
Cross-Tool Normalisation
Operating above SIEM, EDR, BAS, and CTI systems, SecuMap normalises detection logic and validation results without replacing the underlying tooling.
Structured Maturity
Operationalises a structured maturity model aligned with MaGMa principles — from baseline through validation and continuous improvement.
From governance to operational execution
The Detection System of Record defines what healthy detection looks like. Security tools execute detection logic. Validation platforms confirm performance. Infrastructure enables reliable signal generation.
The platform maintains traceability and feedback loops across these domains, ensuring detection health is persistently governed as a system capability.
Execution systems and validation systems: different evidence, one model
SecuMap governs detection capability across tools that do not share the same native metrics. That is expected — and it must not be flattened into a single mistaken schema.
Detection execution systems (for example SIEM, EDR, DLP) produce live alerts and operational outcomes. Evidence typically includes alert volume, true/false positive balance, triage load, and time-based response measures. Validation and simulation systems (for example BAS and controlled purple-team platforms) produce validation evidence — scenarios, pass rates, coverage of tests, and change over time. They do not “fail” as detectors when they have no alert stream; applying alert-only scores to them is a measurement error, not poor performance.
The same threat-to-detection structure still applies: coverage, infrastructure health (here: signal health on the data path and platform health for reliable execution), and effectiveness — with the right measures for each product class. See also validation vs BAS for how simulation evidence should connect to governed outcomes.
| Layer | Detection execution systems | Validation / simulation systems |
|---|---|---|
| Coverage | Rules and controls mapped to priority threats | Scenarios and test scope mapped to the same use cases |
| Infrastructure health | Signal path and platform the product runs on | Test platform health and integration reliability |
| Effectiveness | Alerts, outcomes, analyst reality | Validation results, pass rates, drift, retest history |
What this enables
- System-level visibility into detection health across tools and domains.
- Identification of governance gaps — not just rule gaps.
- Traceable validation-to-execution feedback loops.
- Infrastructure-aware detection reliability and stability monitoring.
- Executive-aligned reporting grounded in measurable health indicators.